description:
A police officer places a GPS device on a suspected drug dealer’s car to trace his whereabouts and build a case against him. A popular retail store uses predictive analytics to send pregnancy-related advertising to a teenager who has yet to tell her parents about her condition. A Kentucky man shoots down a neighbor’s drone that is flying over his private property.
episodes:
01. Security, Liberty, or Neither?
Start by considering the tension between surveillance and the rule of law. While the pace of technological change is extremely rapid, laws are slow to keep up. Worse, the institutions responsible for creating laws often have internal conflicts about the role of privacy and security-as illustrated by a dramatic face-off over John Ashcroft’s hospital bed.
02. The Charlie Hebdo Tragedy
In the wake of the attacks in France, citizens wondered whether their state was taking enough security measures to protect them or doing too much of the wrong thing. In considering this question, review three types of surveillance-physical, electronic and data-and see how each type works. Case studies of the Osama Bin Laden raid and U.S. airport screening show the tension between security and transparency.
03. East Germany's Stasi State
Go inside what is likely the most extreme surveillance state in the history of civilization. It is estimated that, when you count casual informants, as many as one in six East Germans was a spy-keeping tabs on neighbors, friends and family. Survey the history of this insidious surveillance state and think about the lessons it can teach us today.
04. Surveillance in America
See what measures the American government took during the Cold War to prevent our devolution into a Stasi-like state. While the CIA and the FBI had several unauthorized surveillance programs in the 1950s and 1960s, Congress and the Supreme Court stepped in to oversee the intelligence world with several powerful measures in the 1970s.
05. Failing to Connect the Dots on 9/11
After 9/11, the CIA and the FBI were faulted for not sharing intelligence in advance of the attacks. But the two agencies faced stringent legal restrictions on sharing information, going back to the 1978 FISA legislation, which erected a wall” between intelligence gathering and criminal investigations. Review the reasons for and the history of this legislation and the changes that happened after 9/11.”
06. The U.S. Spy Network in Action
Survey the U.S. intelligence community as a whole. Find out how it is structured, how it functions, and how it relates to the rest of the government. Review its methods of gathering and analyzing intelligence, including some of the key challenges in the process.
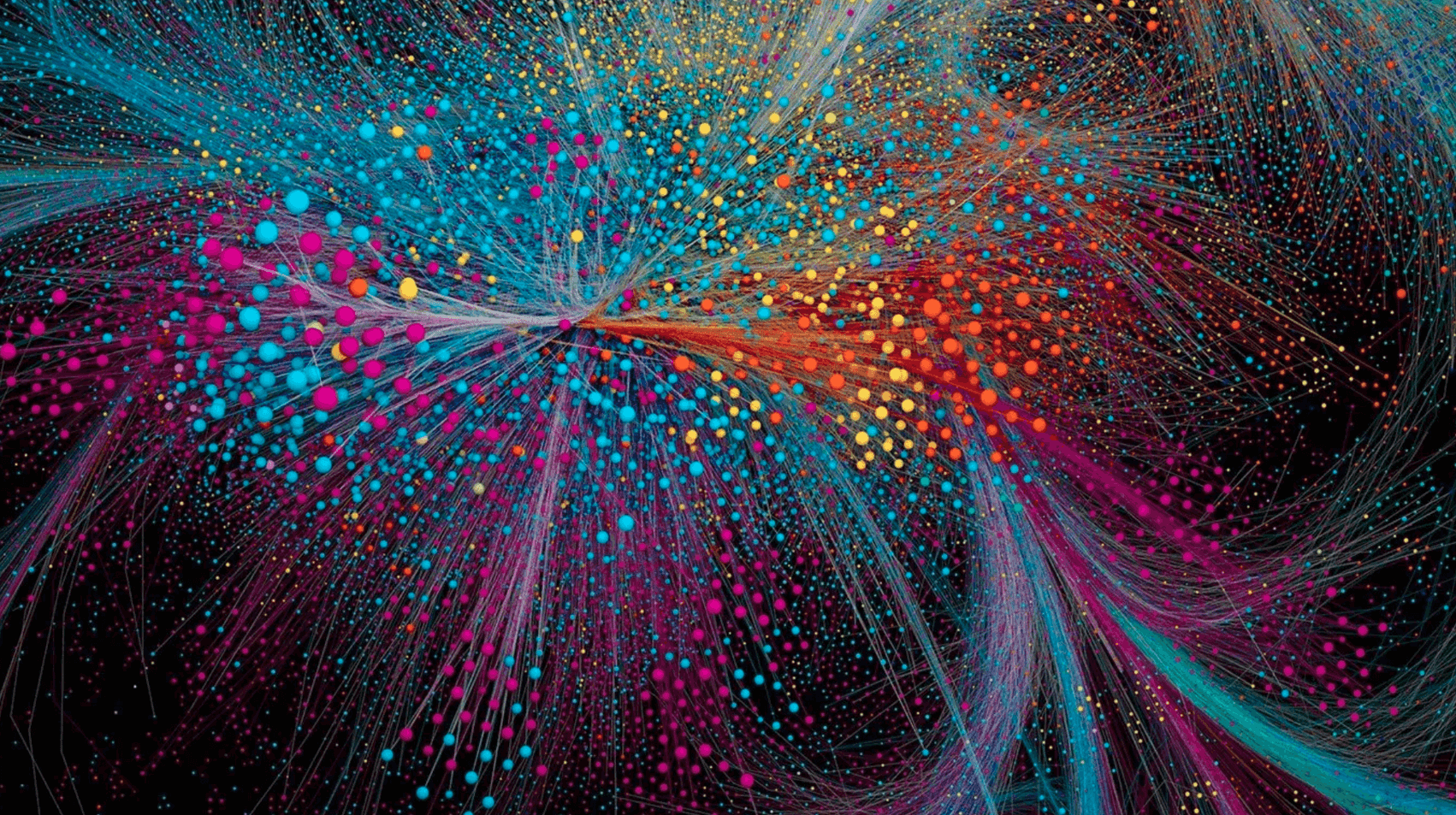
07. Big Data's Shadow
The government and private industries are using a vast cache of information about each of us: our travel patterns, our web browsing habits, our purchasing preferences, and more. Efforts to decide upon and enact laws and policies trail behind new developments in technology, and this lecture examines the potential inherent in such deep and widespread data-as well as the threat it poses to privacy and anonymity.
08. Pushing Long Division to Infinity
If there is something in life you want, then just make it happen!” Following this advice, learn to solve polynomial division problems that have negative terms. Use your new strategy to explore infinite series and Mersenne primes. Then compute infinite sums with the visual approach.”
09. Under Observation: The Panopticon Effect
What happens when we know we are under observation? Or when we know we are anonymous? The observer effect” has a significant psychological impact on someone being watched, whether it is a corporation under public scrutiny or someone chastised on social media. Consider the psychological implications of observation-on both the observed and the observer. ”
10. Drones, Drones Everywhere
Drones-unmanned aerial vehicles-are flooding our skies, bringing with them a variety of concerns about safety and privacy. Review some of the many public and private uses of drones, and then consider policy issues such as: what constitutes permissible use of drone video footage? What safety regulations are appropriate? How can we reconcile civil liberties with the right to privacy?
11. Biometrics: Eyes, Fingers, Everything
Eye scans and facial recognition software were once the purview of science fiction, but now biometric identification is becoming commonplace. Here, examine the different forms of biometric screening, from fingerprinting to DNA analysis. While there are many benefits to this technology, you’ll also see the darker side of this data unleashed in the world.
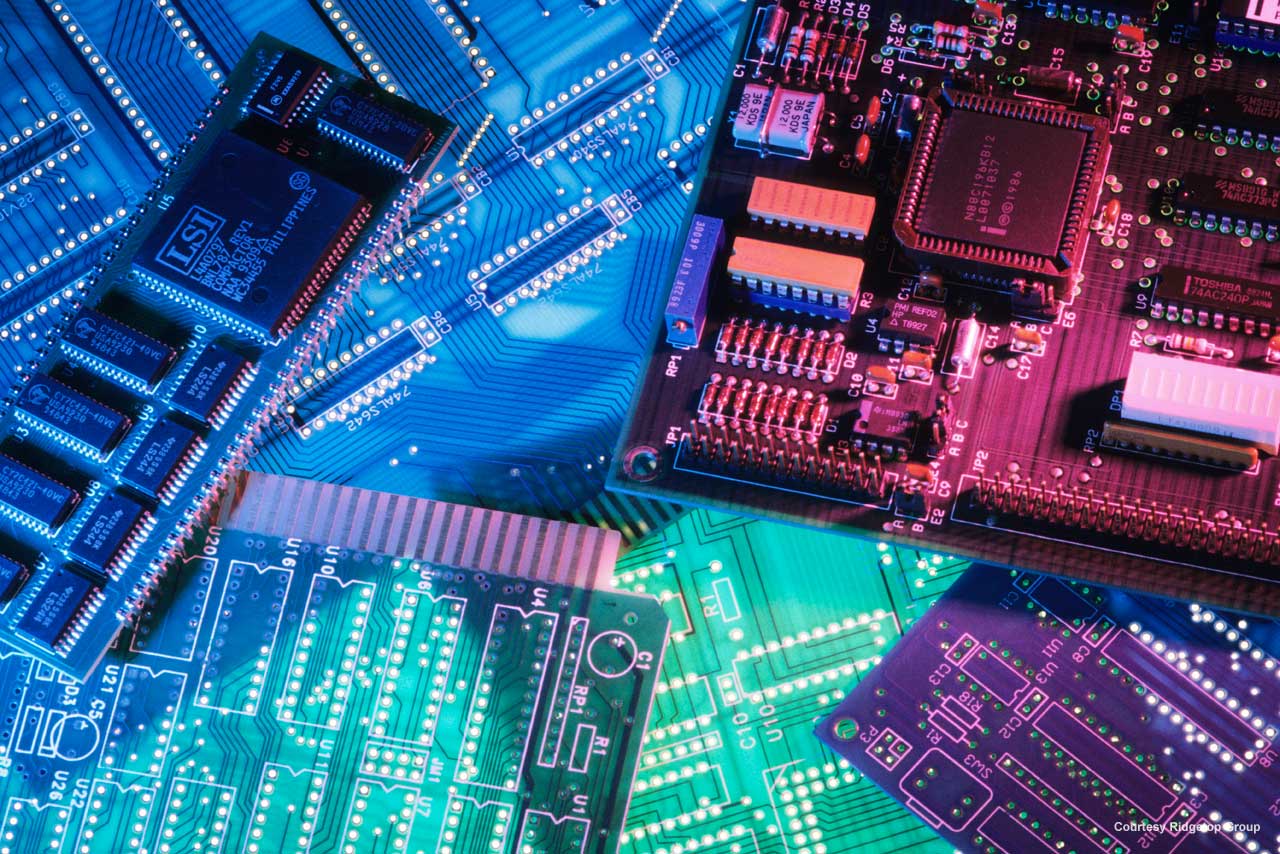
12. Hacking, Espionage, and Surveillance
Spycraft used to be limited to physical surveillance and electronic communications, but now, thanks to the Internet, hacking and digital espionage are the wave of the future. Investigate the techniques by which governments infiltrate each other, ponder the ethics of these actions, and think through the appropriate responses.
13. Local Police on the Cyber Beat
For all the talk about national intelligence programs, local police probably gather more surveillance data than any other governmental entity. Find out what techniques cops use to solve crimes, from closed-circuit cameras to license plate readers, and explore how the NYPD has put all the pieces together.
14. Geolocation: Tracking You and Your Data
You are where you go-at least according to advertisers, divorce attorneys, and criminal investigators. Take a look at how geolocation data is gathered, ranging from the voluntarily given (such as a social media check-in) to the improperly acquired (such as cell phone spying). Then see what investigators can do with such data.
15. Internet Surveillance
Shift your attention to electronic surveillance, and see how the monitoring of web searches and emails allows the government to gain insights into potential security risks from abroad. But even though the surveillance program has oversight, some people fear the potential for abuse is high. Look at both sides of the issue.
16. Metadata: Legal or Not
Dig deeper into the government’s electronic surveillance programs. Here, you’ll learn about metadata”-or data about data. After reviewing what metadata is and how it works, you’ll examine the thorny legal issues surrounding metadata gathering in the years after 9/11, and whether collecting it violates the 4th Amendment protection against search and seizure.”
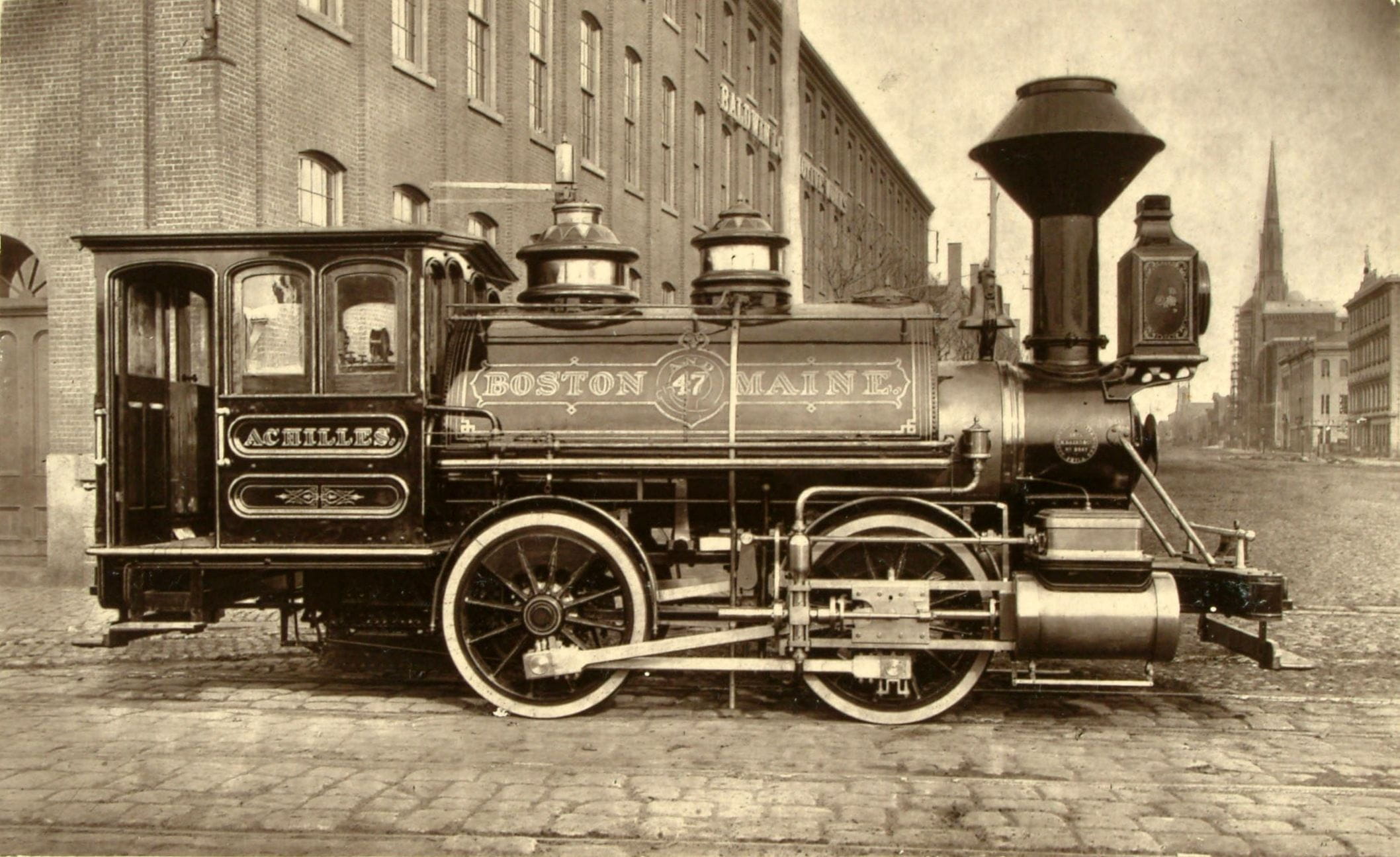
17. Technology Outruns the Law
Continue your study of surveillance and the law with a look at constitutional law. After exploring cases from the 1960s and 1970s about privacy and police informants, you’ll turn to the computer era. Find out what expectations of privacy we have regarding email and phone metadata, airport travel, and our smart phones.
18. Your Personal Data Is the Product
Surveillance dilemmas also play a significant role in the commercial world, where private companies have amassed incredible amounts of data about us. Step into the intriguing world of commercial data aggregation and predictive analytics, and explore the complicated legal and ethical questions surrounding the commercial collection and use of data.
19. The Internet of Things
Technology is quickly transforming our lives with marvelous tools: smart thermostats that automatically adjust the temperature of our homes, self-regulating insulin dispensers, medication management systems, and more. But these technologies come with a cost in terms of the data they aggregate. Who owns the data? How can it be used? What are the responsibilities of the data collectors?
20. Anonymity: Going off the Grid
With the pervasiveness of government and corporate surveillance, some people feel the urge to go off the grid. This lecture explores the benefits and challenges of anonymity for individuals and for society, delving into issues such as the freedom of political speech and the privacy of personal searches and communication. Take a look at two tools people use in pursuit of Internet anonymity: TOR networks and Bitcoin currency.
21. Code Breaking versus Code Making
As privacy has become more of a concern, many technology service providers are instituting more and stronger encryption-including biometric finger scans to unlock phones and access data. But without a back door” for government access, the intelligence community argues, national security is at risk. Unpack the tension from a Fifth Amendment perspective.”
22. Europe's Right to Be Forgotten
Google search results in Europe are different from those in the United States. In Europe, some results are omitted thanks to a right to be forgotten” principle. Although Europe and America’s approach toward privacy is generally similar, here you’ll compare the legal state of data collection in both the public and private realms to find out where the differences lie.”
23. National Security and the First Amendment
The democratization of newsgathering and the expansion of the surveillance state have amplified tensions over the transparency of government operations. Trace the recent history of the news media from the Pentagon Papers to Wikileaks, and draw your own conclusions about what information should be published and who should be allowed to publish it.
24. The Privacy Debate Needs You
Look toward the future and examine the possibilities of quantum computing, human-computer interface, and artificial intelligence. These technological changes are going to require each of us to make decisions about privacy and security-for ourselves and for future generations. Recap what you’ve learned to determine your vision of the best way forward from here.